Machine Trades Print Reading 6th Edition Torrent
| Original author(s) | Bram Cohen |
|---|---|
| Programmer(due south) | Rainberry, Inc. |
| Initial release | 2001 (2001) |
| Repository | github |
| Standard(s) | The BitTorrent Protocol Specification[i] |
| Type | peer-to-peer file sharing |
| Website | www |
BitTorrent is a advice protocol for peer-to-peer file sharing (P2P), which enables users to distribute data and electronic files over the Internet in a decentralized style.
To send or receive files, a person uses a BitTorrent customer on their Internet-connected computer. A BitTorrent client is a computer program that implements the BitTorrent protocol. BitTorrent clients are available for a multifariousness of computing platforms and operating systems, including an official client released by BitTorrent, Inc. Pop clients include μTorrent, Xunlei Thunder,[2] [3] Transmission, qBittorrent, Vuze, Deluge, BitComet and Tixati. BitTorrent trackers provide a list of files available for transfer and allow the client to find peer users, known as "seeds", who may transfer the files.
Developer Bram Cohen designed the protocol in Apr 2001, and released the first available version on two July 2001.[iv] On 15 May 2017, BitTorrent, Inc. (later renamed Rainberry, Inc.) released BitTorrent v2 protocol specification.[5] [6] libtorrent was updated to support the new version on 6 September 2020.[7]
BitTorrent is i of the most common protocols for transferring big files, such as digital video files containing Goggle box shows and video clips, or digital audio files containing songs. As of February 2013,[update] BitTorrent was responsible for three.35% of all worldwide bandwidth—more than half of the vi% of full bandwidth dedicated to file sharing.[8] In 2019, BitTorrent was a ascendant file sharing protocol and generated a substantial amount of Internet traffic, with two.46% of downstream, and 27.58% of upstream traffic.[9] Every bit of 2013[update], BitTorrent had fifteen–27 1000000 concurrent users at any time.[10] As of January 2012[update], BitTorrent is utilized by 150 million agile users. Based on this figure, the total number of monthly users may be estimated to more than a quarter of a billion (≈ 250 million).[11]
The use of BitTorrent may sometimes exist limited past Cyberspace Service Providers (ISPs), on legal or copyright grounds.[ citation needed ] Users may choose to run seedboxes or Virtual Individual Networks (VPNs) to circumvent these restrictions.
History [edit]
| | This department needs expansion. You lot can help by adding to it. (September 2021) |
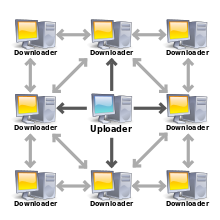
The center computer is interim as a "seed" to provide a file to the other computers which deed equally peers
Programmer Bram Cohen, a University at Buffalo alumnus,[12] designed the protocol in Apr 2001, and released the first bachelor version on two July 2001.[iv]
The start release of the BitTorrent customer had no search engine and no peer exchange. Up until 2005, the only manner to share files was by creating a small text file called a "torrent", that they would upload to a torrent index site. The get-go uploader acted equally a seed, and downloaders would initially connect as peers. Those who wish to download the file would download the torrent, which their client would use to connect to a tracker which had a list of the IP addresses of other seeds and peers in the swarm. Once a peer completed a download of the complete file, it could in turn part every bit a seed. These files incorporate metadata about the files to be shared and the trackers which keep track of the other seeds and peers.
In 2005, first Vuze and so the BitTorrent client introduced distributed tracking using distributed hash tables which allowed clients to commutation data on swarms directly without the demand for a torrent file.
In 2006, peer commutation functionality was added allowing clients to add together peers based on the data institute on connected nodes.
BitTorrent v2 is intended to work seamlessly with previous versions of the BitTorrent protocol. The main reason for the update was that the old cryptographic hash function, SHA-1 is no longer considered safe from malicious attacks by the developers, and as such, v2 uses SHA-256. To ensure backwards compatibility, the v2 .torrent file format supports a hybrid mode where the torrents are hashed through both the new method and the sometime method, with the intent that the files will be shared with peers on both v1 and v2 swarms. Another update to the specification is adding a hash tree to speed upwardly time from adding a torrent to downloading files, and to permit more granular checks for file corruption. In addition, each file is now hashed individually, enabling files in the swarm to exist deduplicated, so that if multiple torrents include the same files, just seeders are only seeding the file from some, downloaders of the other torrents can notwithstanding download the file. Magnet links for v2 as well back up a hybrid mode to ensure support for legacy clients.[13]
Design [edit]

Animation of protocol use: The colored dots beneath each computer in the animation represent different parts of the file being shared. Past the time a copy to a destination computer of each of those parts completes, a copy to another destination computer of that part (or other parts) is already taking place between users.
The BitTorrent protocol can exist used to reduce the server and network impact of distributing large files. Rather than downloading a file from a single source server, the BitTorrent protocol allows users to bring together a "swarm" of hosts to upload and download from each other simultaneously. The protocol is an alternative to the older single source, multiple mirror sources technique for distributing data, and tin piece of work effectively over networks with lower bandwidth. Using the BitTorrent protocol, several basic computers, such as home computers, tin replace big servers while efficiently distributing files to many recipients. This lower bandwidth usage also helps prevent big spikes in internet traffic in a given area, keeping internet speeds college for all users in general, regardless of whether or non they use the BitTorrent protocol.
The file being distributed is divided into segments called pieces. As each peer receives a new piece of the file, information technology becomes a source (of that piece) for other peers, relieving the original seed from having to send that slice to every computer or user wishing a copy. With BitTorrent, the task of distributing the file is shared by those who desire it; it is entirely possible for the seed to ship only a unmarried copy of the file itself and eventually distribute to an unlimited number of peers. Each piece is protected past a cryptographic hash independent in the torrent descriptor.[1] This ensures that any modification of the slice can be reliably detected, and thus prevents both accidental and malicious modifications of any of the pieces received at other nodes. If a node starts with an accurate copy of the torrent descriptor, it tin verify the authenticity of the entire file information technology receives.
Pieces are typically downloaded non-sequentially, and are rearranged into the correct order by the BitTorrent client, which monitors which pieces information technology needs, and which pieces it has and can upload to other peers. Pieces are of the same size throughout a single download (for example, a 10 MB file may be transmitted as ten 1 MB pieces or equally forty 256 KB pieces). Due to the nature of this arroyo, the download of any file can exist halted at whatsoever time and be resumed at a later date, without the loss of previously downloaded information, which in turn makes BitTorrent particularly useful in the transfer of larger files. This also enables the customer to seek out readily available pieces and download them immediately, rather than halting the download and waiting for the next (and maybe unavailable) piece in line, which typically reduces the overall time of the download. This eventual transition from peers to seeders determines the overall "wellness" of the file (as determined by the number of times a file is available in its complete form).
The distributed nature of BitTorrent can atomic number 82 to a flood-like spreading of a file throughout many peer estimator nodes. As more peers join the swarm, the likelihood of a successful download by any particular node increases. Relative to traditional Internet distribution schemes, this permits a significant reduction in the original distributor's hardware and bandwidth resources costs. Distributed downloading protocols in general provide redundancy confronting system problems, reduce dependence on the original distributor,[fourteen] and provide sources for the file which are generally transient and therefore at that place is no single point of failure as in 1 style server-client transfers.
Though both ultimately transfer files over a network, a BitTorrent download differs from a one way server-client download (equally is typical with an HTTP or FTP request, for case) in several fundamental means:
- BitTorrent makes many small data requests over different IP connections to different machines, while server-client downloading is typically made via a unmarried TCP connection to a single machine.
- BitTorrent downloads in a random or in a "rarest-commencement"[xv] approach that ensures loftier availability, while archetype downloads are sequential.
Taken together, these differences allow BitTorrent to achieve much lower cost to the content provider, much college redundancy, and much greater resistance to abuse or to "flash crowds" than regular server software. Nevertheless, this protection, theoretically, comes at a cost: downloads can take time to rise to full speed considering information technology may take time for enough peer connections to exist established, and it may have time for a node to receive sufficient data to go an effective uploader. This contrasts with regular downloads (such every bit from an HTTP server, for instance) that, while more vulnerable to overload and abuse, ascent to full speed very quickly, and maintain this speed throughout. In the start, BitTorrent'southward non-face-to-face download methods made information technology harder to support "streaming playback". In 2014, the client Popcorn Time allowed for streaming of BitTorrent video files. Since and then, more and more than clients are offering streaming options.
Searching [edit]
The BitTorrent protocol provides no fashion to alphabetize torrent files. As a result, a insufficiently small number of websites take hosted a large majority of torrents, many linking to copyrighted works without the authorization of copyright holders, rendering those sites specially vulnerable to lawsuits.[16] A BitTorrent index is a "list of .torrent files, which typically includes descriptions" and data about the torrent'due south content.[17] Several types of websites support the discovery and distribution of data on the BitTorrent network. Public torrent-hosting sites such as The Pirate Bay let users to search and download from their collection of torrent files. Users can typically also upload torrent files for content they wish to distribute. Ofttimes, these sites likewise run BitTorrent trackers for their hosted torrent files, only these two functions are non mutually dependent: a torrent file could be hosted on i site and tracked by some other unrelated site. Private host/tracker sites operate like public ones except that they may restrict admission to registered users and may likewise continue track of the corporeality of data each user uploads and downloads, in an try to reduce "leeching".
Spider web search engines permit the discovery of torrent files that are hosted and tracked on other sites; examples include The Pirate Bay and BTDigg. These sites allow the user to ask for content meeting specific criteria (such as containing a given give-and-take or phrase) and recall a list of links to torrent files matching those criteria. This list tin often be sorted with respect to several criteria, relevance (seeders-leechers ratio) being one of the most popular and useful (due to the way the protocol behaves, the download bandwidth doable is very sensitive to this value). Metasearch engines allow 1 to search several BitTorrent indices and search engines at once.
The Tribler BitTorrent client was amongst the beginning to contain congenital-in search capabilities. With Tribler, users tin can detect .torrent files held by random peers and gustatory modality buddies.[18] Information technology adds such an power to the BitTorrent protocol using a gossip protocol, somewhat like to the eXeem network which was shut down in 2005. The software includes the power to recommend content also. Afterward a dozen downloads, the Tribler software can roughly guess the download gustation of the user, and recommend additional content.[xix]
In May 2007, researchers at Cornell University published a paper proposing a new approach to searching a peer-to-peer network for inexact strings,[20] which could replace the functionality of a central indexing site. A year later, the aforementioned team implemented the system as a plugin for Vuze chosen Cubit[21] and published a follow-up paper reporting its success.[22]
A somewhat similar facility but with a slightly unlike arroyo is provided by the BitComet client through its "Torrent Exchange"[23] feature. Whenever ii peers using BitComet (with Torrent Commutation enabled) connect to each other they exchange lists of all the torrents (name and info-hash) they have in the Torrent Share storage (torrent files which were previously downloaded and for which the user chose to enable sharing past Torrent Substitution). Thus each client builds up a list of all the torrents shared by the peers it connected to in the current session (or it can even maintain the list between sessions if instructed).
At whatsoever fourth dimension the user can search into that Torrent Collection list for a sure torrent and sort the list by categories. When the user chooses to download a torrent from that listing, the .torrent file is automatically searched for (by info-hash value) in the DHT Network and when constitute it is downloaded by the querying client which can subsequently that create and initiate a downloading task.
Downloading and sharing [edit]
Users find a torrent of involvement on a torrent index site or past using a search engine built into the client, download it, and open it with a BitTorrent client. The client connects to the tracker(south) or seeds specified in the torrent file, from which it receives a list of seeds and peers currently transferring pieces of the file(s). The customer connects to those peers to obtain the diverse pieces. If the swarm contains simply the initial seeder, the client connects straight to it, and begins to request pieces. Clients incorporate mechanisms to optimize their download and upload rates.
The effectiveness of this data commutation depends largely on the policies that clients use to determine to whom to ship information. Clients may prefer to send data to peers that send data back to them (a "tit for tat" exchange scheme), which encourages off-white trading. But strict policies ofttimes result in suboptimal situations, such as when newly joined peers are unable to receive any data because they don't accept whatever pieces all the same to trade themselves or when two peers with a proficient connection between them do not commutation information only because neither of them takes the initiative. To counter these effects, the official BitTorrent client program uses a mechanism called "optimistic unchoking", whereby the customer reserves a portion of its bachelor bandwidth for sending pieces to random peers (not necessarily known expert partners, so called preferred peers) in hopes of discovering even better partners and to ensure that newcomers get a take chances to bring together the swarm.[24]
Although "swarming" scales well to tolerate "flash crowds" for popular content, information technology is less useful for unpopular or niche market content. Peers arriving after the initial rush might notice the content unavailable and demand to await for the arrival of a "seed" in guild to consummate their downloads. The seed inflow, in turn, may take long to happen (this is termed the "seeder promotion problem"). Since maintaining seeds for unpopular content entails loftier bandwidth and administrative costs, this runs counter to the goals of publishers that value BitTorrent every bit a cheap alternative to a client-server arroyo. This occurs on a huge calibration; measurements accept shown that 38% of all new torrents go unavailable within the commencement month.[25] A strategy adopted past many publishers which significantly increases availability of unpopular content consists of bundling multiple files in a single swarm.[26] More sophisticated solutions accept also been proposed; by and large, these use cantankerous-torrent mechanisms through which multiple torrents tin cooperate to meliorate share content.[27]
Creating and publishing [edit]
| | This article needs to be updated. The reason given is: Some extensions described in this section as experimental have been standardized. This section is factually incorrect about some aspects of v1 and v2.. (January 2022) |
The peer distributing a data file treats the file as a number of identically sized pieces, usually with byte sizes of a ability of 2, and typically between 32 kB and xvi MB each. The peer creates a hash for each piece, using the SHA-1 hash function, and records it in the torrent file. Pieces with sizes greater than 512 kB will reduce the size of a torrent file for a very large payload, but is claimed to reduce the efficiency of the protocol.[28] When another peer afterward receives a detail piece, the hash of the piece is compared to the recorded hash to test that the piece is error-free.[1] Peers that provide a complete file are called seeders, and the peer providing the initial copy is called the initial seeder. The exact information contained in the torrent file depends on the version of the BitTorrent protocol.
Past convention, the name of a torrent file has the suffix .torrent. Torrent files have an "denote" section, which specifies the URL of the tracker, and an "info" department, containing (suggested) names for the files, their lengths, the piece length used, and a SHA-1 hash code for each slice, all of which are used by clients to verify the integrity of the data they receive. Though SHA-one has shown signs of cryptographic weakness, Bram Cohen did not initially consider the risk large plenty for a backward incompatible modify to, for example, SHA-iii. As of BitTorrent v2 the hash role has been updated to SHA-256.[29]
In the early days, torrent files were typically published to torrent index websites, and registered with at least ane tracker. The tracker maintained lists of the clients currently continued to the swarm.[1] Alternatively, in a trackerless system (decentralized tracking) every peer acts as a tracker. Azureus was the first[30] BitTorrent client to implement such a system through the distributed hash tabular array (DHT) method. An alternative and incompatible DHT system, known as Mainline DHT, was released in the Mainline BitTorrent customer iii weeks later (though it had been in evolution since 2002)[thirty] and subsequently adopted past the μTorrent, Transmission, rTorrent, KTorrent, BitComet, and Deluge clients.
After the DHT was adopted, a "individual" flag – analogous to the broadcast flag – was unofficially introduced, telling clients to restrict the utilize of decentralized tracking regardless of the user's desires.[31] The flag is intentionally placed in the info section of the torrent so that information technology cannot be disabled or removed without changing the identity of the torrent. The purpose of the flag is to prevent torrents from being shared with clients that do not have admission to the tracker. The flag was requested for inclusion in the official specification in August 2008, but has non been accepted even so.[32] Clients that have ignored the private flag were banned by many trackers, discouraging the exercise.[33]
Anonymity [edit]
BitTorrent does not, on its own, offer its users anonymity. One can usually come across the IP addresses of all peers in a swarm in 1's ain client or firewall program. This may betrayal users with insecure systems to attacks.[24] In some countries, copyright organizations scrape lists of peers, and send takedown notices to the internet service provider of users participating in the swarms of files that are under copyright. In some jurisdictions, copyright holders may launch lawsuits against uploaders or downloaders for infringement, and police may arrest suspects in such cases.
Various means have been used to promote anonymity. For example, the BitTorrent client Tribler makes available a Tor-similar onion network, optionally routing transfers through other peers to obscure which customer has requested the information. The get out node would be visible to peers in a swarm, but the Tribler system provides go out nodes. One advantage of Tribler is that clearnet torrents can be downloaded with only a small decrease in download speed from one "hop" of routing.
i2p provides a like anonymity layer although in that case, 1 tin merely download torrents that have been uploaded to the i2p network.[34] The bittorrent client Vuze allows users who are not concerned nigh anonymity to take clearnet torrents, and make them available on the i2p network.[35]
Most BitTorrent clients are not designed to provide anonymity when used over Tor,[36] and in that location is some debate equally to whether torrenting over Tor acts as a drag on the network.[37]
Private torrent trackers are unremarkably invitation but, and require members to participate in uploading, but have the downside of a unmarried centralized point of failure. Oink'due south Pink Palace and What.cd are examples of individual trackers which have been close downward.
Seedbox services download the torrent files first to the visitor'south servers, assuasive the user to directly download the file from there.[38] [39] One's IP accost would be visible to the Seedbox provider, simply non to third parties.
Virtual private networks encrypt transfers, and substitute a different IP accost for the user'south, so that anyone monitoring a torrent swarm volition simply see that address.
Associated technologies [edit]
Distributed trackers [edit]
On two May 2005, Azureus 2.iii.0.0 (now known as Vuze) was released,[xl] introducing support for "trackerless" torrents through a system called the "distributed database." This organisation is a Distributed hash table implementation which allows the client to utilise torrents that do not take a working BitTorrent tracker. Instead just bootstrapping server is used (router.bittorrent.com, dht.transmissionbt.com or router.utorrent.com[41] [42]). The following calendar month, BitTorrent, Inc. released version four.2.0 of the Mainline BitTorrent client, which supported an culling DHT implementation (popularly known every bit "Mainline DHT", outlined in a draft on their website) that is incompatible with that of Azureus. In 2014, measurement showed concurrent users of Mainline DHT to be from ten million to 25 million, with a daily churn of at least 10 one thousand thousand.[43]
Current versions of the official BitTorrent client, μTorrent, BitComet, Transmission and BitSpirit all share compatibility with Mainline DHT. Both DHT implementations are based on Kademlia.[44] As of version 3.0.v.0, Azureus also supports Mainline DHT in addition to its ain distributed database through utilise of an optional application plugin.[45] This potentially allows the Azureus/Vuze customer to reach a bigger swarm.
Another idea that has surfaced in Vuze is that of virtual torrents. This idea is based on the distributed tracker approach and is used to depict some web resource. Currently, it is used for instant messaging. It is implemented using a special messaging protocol and requires an appropriate plugin. Anatomic P2P is some other approach, which uses a decentralized network of nodes that route traffic to dynamic trackers. Near BitTorrent clients also employ Peer exchange (PEX) to gather peers in addition to trackers and DHT. Peer exchange checks with known peers to meet if they know of any other peers. With the 3.0.5.0 release of Vuze, all major BitTorrent clients now accept compatible peer exchange.
Spider web seeding [edit]
Web "seeding" was implemented in 2006 every bit the ability of BitTorrent clients to download torrent pieces from an HTTP source in addition to the "swarm". The advantage of this feature is that a website may distribute a torrent for a particular file or batch of files and brand those files available for download from that same spider web server; this can simplify long-term seeding and load balancing through the use of existing, inexpensive, web hosting setups. In theory, this would make using BitTorrent nearly as piece of cake for a web publisher every bit creating a straight HTTP download. In add-on, it would allow the "web seed" to be disabled if the swarm becomes too pop while still allowing the file to be readily available. This feature has two distinct specifications, both of which are supported by Libtorrent and the 26+ clients that use it.
The beginning was created by John "TheSHAD0W" Hoffman, who created BitTornado.[46] [47] This first specification requires running a spider web service that serves content by info-hash and piece number, rather than filename.
The other specification is created by GetRight authors and can rely on a basic HTTP download space (using byte serving).[48] [49]
In September 2010, a new service named Burnbit was launched which generates a torrent from any URL using webseeding.[50] There are server-side solutions that provide initial seeding of the file from the web server via standard BitTorrent protocol and when the number of external seeders attain a limit, they finish serving the file from the original source.[51]
[edit]
A technique called broadcatching combines RSS feeds with the BitTorrent protocol to create a content delivery arrangement, further simplifying and automating content distribution. Steve Gillmor explained the concept in a column for Ziff-Davis in December 2003.[52] The discussion spread quickly among bloggers (Ernest Miller,[53] Chris Pirillo, etc.). In an article entitled Broadcatching with BitTorrent, Scott Raymond explained:
I want RSS feeds of BitTorrent files. A script would periodically cheque the feed for new items, and use them to beginning the download. Then, I could observe a trusted publisher of an Alias RSS feed, and "subscribe" to all new episodes of the prove, which would then start downloading automatically – like the "season laissez passer" characteristic of the TiVo.
—Scott Raymond, scottraymond.net[54]
The RSS feed will track the content, while BitTorrent ensures content integrity with cryptographic hashing of all data, and so feed subscribers will receive uncorrupted content. One of the first and popular software clients (free and open source) for broadcatching is Miro. Other free software clients such as PenguinTV and KatchTV are also now supporting broadcatching. The BitTorrent web-service MoveDigital added the ability to make torrents available to any web application capable of parsing XML through its standard REST-based interface in 2006,[55] though this has since been discontinued. Additionally, Torrenthut is developing a similar torrent API that will provide the same features, and help bring the torrent customs to Web 2.0 standards. Aslope this release is a first PHP application congenital using the API called PEP, which will parse any Really Simple Syndication (RSS ii.0) feed and automatically create and seed a torrent for each enclosure found in that feed.[56]
Throttling and encryption [edit]
Since BitTorrent makes up a big proportion of total traffic, some ISPs accept chosen to "throttle" (deadening down) BitTorrent transfers. For this reason, methods take been adult to disguise BitTorrent traffic in an try to thwart these efforts.[57] Protocol header encrypt (PHE) and Message stream encryption/Protocol encryption (MSE/PE) are features of some BitTorrent clients that try to brand BitTorrent difficult to detect and throttle. As of Nov 2015, Vuze, Bitcomet, KTorrent, Transmission, Deluge, μTorrent, MooPolice, Halite, qBittorrent, rTorrent, and the latest official BitTorrent client (v6) support MSE/PE encryption.
In August 2007, Comcast was preventing BitTorrent seeding by monitoring and interfering with the communication betwixt peers. Protection confronting these efforts is provided past proxying the client-tracker traffic via an encrypted tunnel to a point exterior of the Comcast network.[58] In 2008, Comcast chosen a "truce" with BitTorrent, Inc. with the intention of shaping traffic in a protocol-doubter mode.[59] Questions nearly the ideals and legality of Comcast'southward behavior accept led to renewed debate most net neutrality in the United States.[60] In general, although encryption can make it hard to determine what is being shared, BitTorrent is vulnerable to traffic analysis. Thus, fifty-fifty with MSE/PE, it may be possible for an Internet access provider to recognize BitTorrent and likewise to determine that a organisation is no longer downloading but only uploading information, and terminate its connexion by injecting TCP RST (reset flag) packets.
Multitrackers [edit]
Some other unofficial feature is an extension to the BitTorrent metadata format proposed by John Hoffman[61] and implemented by several indexing websites. It allows the use of multiple trackers per file, so if one tracker fails, others tin can continue to support file transfer. It is implemented in several clients, such as BitComet, BitTornado, BitTorrent, KTorrent, Transmission, Deluge, μTorrent, rtorrent, Vuze, and Frostwire. Trackers are placed in groups, or tiers, with a tracker randomly chosen from the summit tier and tried, moving to the side by side tier if all the trackers in the meridian tier fail.
Torrents with multiple trackers can subtract the time it takes to download a file, merely also have a few consequences:
- Poorly implemented[62] clients may contact multiple trackers, leading to more than overhead-traffic.
- Torrents from closed trackers of a sudden become downloadable past non-members, every bit they can connect to a seed via an open up tracker.
Peer selection [edit]
As of Dec 2008,[update] BitTorrent, Inc. was working with Oversi on new Policy Find Protocols that query the ISP for capabilities and network architecture information. Oversi's Isp hosted NetEnhancer box is designed to "ameliorate peer pick" by helping peers find local nodes, improving download speeds while reducing the loads into and out of the ISP's network.[63]
Implementations [edit]
The BitTorrent specification is free to use and many clients are open up source, so BitTorrent clients accept been created for all common operating systems using a diverseness of programming languages. The official BitTorrent client, μTorrent, qBittorrent, Manual, Vuze, and BitComet are some of the well-nigh popular clients.[64] [65] [66] [67]
Some BitTorrent implementations such equally MLDonkey and Torrentflux are designed to run as servers. For instance, this can be used to centralize file sharing on a single dedicated server which users share access to on the network.[68] Server-oriented BitTorrent implementations can also be hosted past hosting providers at co-located facilities with high bandwidth Internet connectivity (e.g., a datacenter) which can provide dramatic speed benefits over using BitTorrent from a regular home broadband connexion. Services such as ImageShack tin download files on BitTorrent for the user, allowing them to download the unabridged file by HTTP once it is finished.
The Opera web browser supports BitTorrent natively.[69] Brave web browser ships with an extension which supports WebTorrent, a BitTorrent-like protocol based on WebRTC instead of UDP and TCP.[seventy] [71] BitLet allowed users to download Torrents directly from their browser using a Java applet (until browsers removed support for Java applets).[72] [ citation needed ] An increasing number of hardware devices are being made to support BitTorrent. These include routers and NAS devices containing BitTorrent-capable firmware like OpenWrt. Proprietary versions of the protocol which implement DRM, encryption, and authentication are plant within managed clients such as Pando.
Adoption [edit]
A growing number of individuals and organizations are using BitTorrent to distribute their own or licensed works (due east.chiliad. indie bands distributing digital files of their new songs). Independent adopters report that BitTorrent engineering science reduces demands on private networking hardware and bandwidth, an essential for not-profit groups with big amounts of cyberspace traffic.[73]
Some uses of BitTorrent for file sharing may violate laws in some jurisdictions (see legislation section).
Film, video, and music [edit]
- BitTorrent Inc. has obtained a number of licenses from Hollywood studios for distributing pop content from their websites.[ citation needed ]
- Sub Pop Records releases tracks and videos via BitTorrent Inc.[74] to distribute its one thousand+ albums. Babyshambles and The Libertines (both bands associated with Pete Doherty) have extensively used torrents to distribute hundreds of demos and live videos. US industrial rock band Nine Inch Nails often distributes albums via BitTorrent.
- Podcasting software is starting to integrate BitTorrent to help podcasters deal with the download demands of their MP3 "radio" programs. Specifically, Juice and Miro (formerly known as Democracy Role player) support automatic processing of .torrent files from RSS feeds. Similarly, some BitTorrent clients, such equally μTorrent, are able to process web feeds and automatically download content found within them.
- DGM Live purchases are provided via BitTorrent.[75]
- VODO, a service which distributes "complimentary-to-share" movies and Television set shows via BitTorrent.[76] [77] [78]
Broadcasters [edit]
- In 2008, the CBC became the first public broadcaster in North America to make a total show (Canada's Side by side Great Prime number Minister) available for download using BitTorrent.[79]
- The Norwegian Dissemination Corporation (NRK) has since March 2008 experimented with bittorrent distribution, available online.[80] Only selected works in which NRK owns all royalties are published. Responses have been very positive, and NRK is planning to offer more than content.
- The Dutch VPRO broadcasting organization released four documentaries in 2009 and 2010 under a Creative Commons license using the content distribution characteristic of the Mininova tracker.[81] [82] [83]
Cloud Service Providers [edit]
- The Amazon AWS's Simple Storage Service (S3), until April 29, 2021, had supported sharing of bucket objects with BitTorrent protocols. As of June thirteen, 2020, the characteristic is only bachelor in service regions launched after May 30, 2016.[84] [85] [86] The feature for the existing customers volition be extended for an additional 12 months post-obit the deprecation. After Apr 29, 2022, BitTorrent clients volition no longer connect to Amazon S3.
Software [edit]
- Blizzard Amusement uses BitTorrent (via a proprietary client called the "Blizzard Downloader", associated with the Blizzard "BattleNet" network) to distribute content and patches for Diablo III, StarCraft Ii and World of Warcraft, including the games themselves.[87]
- Wargaming uses BitTorrent in their popular titles World of Tanks, World of Warships and World of Warplanes to distribute game updates.[88]
- CCP Games, maker of the space simulation MMORPG Eve Online, has announced that a new launcher will be released that is based on BitTorrent.[89] [90]
- Many software games, especially those whose big size makes them difficult to host due to bandwidth limits, extremely frequent downloads, and unpredictable changes in network traffic, will distribute instead a specialized, stripped down BitTorrent client with enough functionality to download the game from the other running clients and the master server (which is maintained in instance not plenty peers are available).
- Many major open source and free software projects encourage BitTorrent too every bit conventional downloads of their products (via HTTP, FTP etc.) to increase availability and to reduce load on their own servers, peculiarly when dealing with larger files.[91]
- Resilio Sync is a BitTorrent-based[92] binder-syncing tool which can act equally an alternative to server-based synchronisation services such every bit Dropbox.
Government [edit]
- The British government used BitTorrent to distribute details well-nigh how the tax money of British citizens was spent.[93] [94]
Teaching [edit]
- Florida Land Academy uses BitTorrent to distribute big scientific data sets to its researchers.[95]
- Many universities that have BOINC distributed calculating projects have used the BitTorrent functionality of the client-server organisation to reduce the bandwidth costs of distributing the customer-side applications used to process the scientific data. If a BOINC distributed computing awarding needs to be updated (or merely sent to a user), it can practice so with little affect on the BOINC server.[96]
- The developing Human being Connectome Project uses BitTorrent to share their open up dataset.[97]
- Bookish Torrents is a BitTorrent tracker for use by researchers in fields that need to share large datasets[98] [99]
Others [edit]
- Facebook uses BitTorrent to distribute updates to Facebook servers.[100]
- Twitter uses BitTorrent to distribute updates to Twitter servers.[101] [102]
- The Net Archive added BitTorrent to its file download options for over ane.3 million existing files, and all newly uploaded files, in August 2012.[103] [104] This method is the fastest means of downloading media from the Archive.[103] [105]
By early 2015, AT&T estimated that BitTorrent accounted for 20% of all broadband traffic.[106]
Routers that utilize network address translation (NAT) must maintain tables of source and destination IP addresses and ports. Because BitTorrent frequently contacts 20–xxx servers per second, the NAT tables of some consumer-form routers are chop-chop filled. This is a known crusade of some home routers ceasing to piece of work correctly.[107] [108]
Legislation [edit]
Although the protocol itself is legal,[109] bug stalk from using the protocol to traffic copyright infringing works, since BitTorrent is frequently used to download otherwise paid content, such as movies and video games. In that location has been much controversy over the use of BitTorrent trackers. BitTorrent metafiles themselves do not store file contents. Whether the publishers of BitTorrent metafiles violate copyrights by linking to copyrighted works without the authorization of copyright holders is controversial. Diverse jurisdictions have pursued legal action against websites that host BitTorrent trackers.
High-profile examples include the endmost of Suprnova.org, TorrentSpy, LokiTorrent, BTJunkie, Mininova, Oink's Pink Palace and What.cd. BitTorrent search engine The Pirate Bay torrent website, formed by a Swedish group, is noted for the "legal" section of its website in which messages and replies on the subject of alleged copyright infringements are publicly displayed. On 31 May 2006, The Pirate Bay'due south servers in Sweden were raided by Swedish police on allegations by the MPAA of copyright infringement;[110] still, the tracker was up and running over again iii days later. In the report used to value NBC Universal in its merger with Comcast, Envisional examined the ten,000 torrent swarms managed past PublicBT which had the most agile downloaders. After excluding pornographic and unidentifiable content, information technology was establish that only ane swarm offered legitimate content.[111]
In the United States, more 200,000 lawsuits have been filed for copyright infringement on BitTorrent since 2010.[112] In the Great britain, on 30 April 2012, the Loftier Courtroom of Justice ordered five ISPs to block The Pirate Bay.[113]
Security [edit]
One concern is the UDP flood attack. BitTorrent implementations oftentimes use μTP for their communication. To accomplish high bandwidths, the underlying protocol used is UDP, which allows spoofing of source addresses of internet traffic. It has been possible to comport out Denial-of-service attacks in a P2P lab environment, where users running BitTorrent clients act as amplifiers for an attack at another service.[114] Yet this is not ever an constructive attack considering ISPs can check if the source accost is correct.
Several studies on BitTorrent constitute files bachelor for download containing malware. In particular, i pocket-size sample indicated that 18% of all executable programs available for download contained malware.[115] Some other study claims that equally much equally 14.five% of BitTorrent downloads comprise nix-24-hour interval malware, and that BitTorrent was used as the distribution mechanism for 47% of all cipher-day malware they take found.[116]
See also [edit]
- Anonymous P2P
- Anti-Counterfeiting Merchandise Agreement
- Bencode
- Cache Discovery Protocol
- Comparison of BitTorrent clients
- Comparison of BitTorrent sites
- Comparing of BitTorrent tracker software
- Glossary of BitTorrent terms
- Magnet URI scheme
- Simple file verification
- Super-seeding
- Torrent poisoning
References [edit]
- ^ a b c d Cohen, Bram (October 2002). "BitTorrent Protocol ane.0". BitTorrent.org. Archived from the original on 8 Feb 2014. Retrieved 1 June 2020.
- ^ Van der Sar, Ernesto (iv December 2009). "Thunder Blasts uTorrent'due south Marketplace Share Away - TorrentFreak". TorrentFreak. Archived from the original on 20 Feb 2016. Retrieved xviii June 2018.
- ^ "迅雷-全球共享计算与区块链创领者". Xunlei.com. Archived from the original on 18 November 2019. Retrieved 21 November 2019.
- ^ a b Cohen, Bram (2 July 2001). "BitTorrent – a new P2P app". Yahoo eGroups. Archived from the original on 29 Jan 2008. Retrieved 15 April 2007.
- ^ "Merge pull request #59 from the8472/new-hash-algos". BitTorrent. 15 May 2017. Archived from the original on 10 Nov 2021. Retrieved 13 September 2021.
- ^ Cohen, Bram. "The BitTorrent Protocol Specification v2". BitTorrent.org. BitTorrent. Archived from the original on 12 Nov 2020. Retrieved 28 October 2020.
- ^ Norberg, Arvid (7 September 2020). "Bittorrent-v2". libtorrent.org. libtorrent. Archived from the original on 30 October 2020. Retrieved 28 Oct 2020.
- ^ "Application Usage & Threat Report". Palo Alto Networks. 2013. Archived from the original on 31 Oct 2013. Retrieved 7 April 2013.
- ^ Marozzo, Fabrizio; Talia, Domenico; Trunfio, Paolo (2020). "A Sleep-and-Wake technique for reducing energy consumption in BitTorrent networks". Concurrency and Computation: Practice and Experience. 32 (xiv). doi:10.1002/cpe.5723. ISSN 1532-0634. S2CID 215841734.
- ^ Wang, Liang; Kangasharju, J. (1 September 2013). "Measuring large-scale distributed systems: Case of Bit Torrent Mainline DHT". IEEE P2P 2013 Proceedings. pp. 1–ten. doi:10.1109/P2P.2013.6688697. ISBN978-1-4799-0515-vii. S2CID 5659252. Archived from the original on eighteen November 2015. Retrieved vii January 2016.
- ^ "BitTorrent and μTorrent Software Surpass 150 Million User Milestone". Bittorrent.com. 9 Jan 2012. Archived from the original on 26 March 2014. Retrieved 9 July 2012.
- ^ "UB Engineering Tweeter". Academy at Buffalo's Schoolhouse of Engineering and Applied Sciences. Archived from the original on 11 November 2013. Retrieved 4 Jan 2022.
- ^ "Bittorrent-v2". libbittorrent.org. libbittorrent. Archived from the original on 30 October 2020. Retrieved 28 Oct 2020.
- ^ Menasche, Daniel S.; Rocha, Antonio A. A.; de Souza e Silva, Edmundo A.; Leao, Rosa M.; Towsley, Don; Venkataramani, Arun (2010). "Estimating Cocky-Sustainability in Peer-to-Peer Swarming Systems". Performance Evaluation. 67 (11): 1243–1258. arXiv:1004.0395. doi:10.1016/j.peva.2010.08.013. S2CID 9361889. by D. Menasche, A. Rocha, E. de Souza e Silva, R. M. Leao, D. Towsley, A. Venkataramani.
- ^ Urvoy-Keller (December 2006). "Rarest First and Choke Algorithms Are Plenty" (PDF). SIGCOMM. Archived (PDF) from the original on 23 May 2012. Retrieved 9 March 2012.
- ^ Ernesto (12 July 2009). "PublicBT Tracker Set up To Patch BitTorrent' Achilles' Heel". Torrentfreak. Archived from the original on 26 March 2014. Retrieved 14 July 2009.
- ^ Chwan-Hwa (John) Wu, J. David Irwin. Introduction to Computer Networks and Cybersecurity. Chapter 5.iv.: Partially Centralized Architectures. CRC Press. 4 February 2013. ISBN 9781466572133
- ^ Zeilemaker, N., Capotă, K., Bakker, A., & Pouwelse, J. (2011). "Tribler P2P Media Search and Sharing." Proceedings of the 19th ACM International Conference on Multimedia - MM '11.
- ^ "DecentralizedRecommendation –". Tribler.org. Archived from the original on 2 December 2008. Retrieved 9 July 2012.
- ^ Wong, Bernard; Vigfusson, Ymir; Gun Sirer, Emin (2 May 2007). "Hyperspaces for Object Clustering and Judge Matching in Peer-to-Peer Overlays" (PDF). Cornell University. Archived (PDF) from the original on 17 June 2012. Retrieved 7 April 2013.
- ^ Wong, Bernard (2008). "Cubit: Approximate Matching for Peer-to-Peer Overlays". Cornell University. Archived from the original on 31 December 2012. Retrieved 26 May 2008.
- ^ Wong, Bernard. "Gauge Matching for Peer-to-Peer Overlays with Cubit" (PDF). Cornell University. Archived (PDF) from the original on 29 October 2008. Retrieved 26 May 2008.
- ^ "Torrent Substitution". Archived from the original on 5 October 2013. Retrieved 31 January 2010.
The torrent sharing feature of BitComet. Bitcomet.com.
- ^ a b Tamilmani, Karthik (25 October 2003). "Studying and enhancing the BitTorrent protocol". Stony Brook University. Archived from the original (DOC) on nineteen November 2004. Retrieved 6 May 2006.
- ^ Kaune, Sebastian; et al. (2009). "Unraveling BitTorrent's File Unavailability: Measurements and Analysis". arXiv:0912.0625 [cs.NI].
- ^ D. Menasche; et al. (1–four December 2009). Content Availability and Bundling in Swarming Systems (PDF). CoNEXT'09. Rome, Italian republic: ACM via sigcomm.org. ISBN978-i-60558-636-6. Archived (PDF) from the original on 1 May 2011. Retrieved eighteen Dec 2009.
- ^ Kaune, Sebastian; et al. "The Seeder Promotion Problem: Measurements, Assay and Solution Space" (PDF). Queen Mary's University London. Archived (PDF) from the original on ix August 2014. Retrieved twenty July 2017.
- ^ "BitTorrent Specification". Wiki.theory.org. Archived from the original on 26 June 2013. Retrieved 9 July 2012. [ dubious ]
- ^ "» BitTorrent v2". Archived from the original on 27 September 2020. Retrieved 27 September 2020.
- ^ a b Jones, Ben (7 June 2015). "BitTorrent's DHT Turns x Years Old". TorrentFreak. Archived from the original on 11 June 2015. Retrieved 5 July 2015.
- ^ "Unofficial BitTorrent Protocol Specification v1.0". Archived from the original on 14 Dec 2006. Retrieved four Oct 2009. [ dubious ]
- ^ Harrison, David (3 August 2008). "Private Torrents". Bittorrent.org. Archived from the original on 24 March 2013. Retrieved iv October 2009.
- ^ "BitComet Banned From Growing Number of Private Trackers". Archived from the original on 26 March 2014. Retrieved iv October 2009.
- ^ "I2P Compared to Tor - I2P". Archived from the original on 22 December 2015. Retrieved 16 December 2015.
- ^ "I2PHelper HowTo - VuzeWiki". Archived from the original on twenty October 2017. Retrieved sixteen Dec 2015.
- ^ "Bittorrent over Tor isn't a good idea - The Tor Weblog". Archived from the original on 13 October 2016. Retrieved two October 2016.
- ^ Inc., The Tor Project. "Tor Projection: FAQ". Archived from the original on 22 October 2016. Retrieved 2 Oct 2016.
- ^ "This Website Could Exist The Ultimate All-In-I Torrent Automobile". 8 April 2016. Archived from the original on 8 Apr 2016.
- ^ "Torrent From the Cloud With Seedr - TorrentFreak". 17 January 2016. Archived from the original on 19 April 2016. Retrieved viii April 2016.
- ^ "Vuze Changelog". Azureus.sourceforge.net. Archived from the original on 1 December 2006.
- ^ "DHT Bootstrap Update | The BitTorrent Engineering science Weblog". engineering.bittorrent.com. Archived from the original on 14 December 2019. Retrieved 21 Nov 2019.
- ^ GitHub - bittorrent/bootstrap-dht: DHT bootstrap server, BitTorrent Inc., xi November 2019, archived from the original on xiv January 2020, retrieved 21 November 2019
- ^ Wang, Liang; Kangasharju, Jussi. (2013). "Measuring Large-Scale Distributed Systems: Instance of BitTorrent Mainline DHT" (PDF). IEEE Peer-to-Peer. Archived (PDF) from the original on 12 May 2014. Retrieved 15 May 2014.
- ^ "Khashmir.SourceForge.internet". Khashmir.SourceForge.cyberspace. Archived from the original on 2 July 2012. Retrieved 9 July 2012.
- ^ "plugins.vuze.com". plugins.vuze.com. Archived from the original on 1 August 2012. Retrieved 9 July 2012.
- ^ "HTTP-Based Seeding Specification". BitTornado.com. Archived from the original (TXT) on 20 March 2004. Retrieved ix May 2006.
- ^ John Hoffman, DeHackEd (25 February 2008). "HTTP Seeding – BitTorrent Enhancement Proposal № 17". Archived from the original on thirteen December 2013. Retrieved 17 February 2012.
- ^ "HTTP/FTP Seeding for BitTorrent". GetRight.com. Archived from the original on 28 December 2009. Retrieved 18 March 2010.
- ^ Michael Burford (25 February 2008). "WebSeed – HTTP/FTP Seeding (GetRight fashion) – BitTorrent Enhancement Proposal № 19". Bittorrent.org. Archived from the original on 13 Dec 2013. Retrieved 17 February 2012.
- ^ "Burn Whatsoever Spider web-Hosted File into a Torrent With Burnbit". TorrentFreak. thirteen September 2010. Archived from the original on 9 August 2011. Retrieved 9 July 2012.
- ^ "PHP based torrent file creator, tracker and seed server". PHPTracker. Archived from the original on 19 December 2013. Retrieved 9 July 2012.
- ^ Gillmor, Steve (thirteen December 2003). "BitTorrent and RSS Create Confusing Revolution". EWeek.com. fourteen December 2003. Retrieved 22 April 2007.
- ^ Miller, Ernest (2 March 2004). "BitTorrent + RSS = The New Circulate". Archived from the original on 23 October 2013. . The Importance of... Corante.com.
- ^ Raymond, Scott (16 December 2003). "Broadcatching with BitTorrent". scottraymond.internet. Archived from the original on thirteen February 2004.
- ^ "MoveDigital API Residual functions". Move Digital. 2006. Archived from the original on 11 August 2006. Retrieved nine May 2006. Documentation.
- ^ "Prodigem Enclosure Puller(pep.txt)". Prodigem.com. Archived from the original (TXT) on 26 May 2006. Retrieved 9 May 2006. via Net Wayback Car.
- ^ "Encrypting Bittorrent to have out traffic shapers". Torrentfreak.com. 5 Feb 2006. Archived from the original on 26 March 2014. Retrieved ix May 2006.
- ^ "Comcast Throttles BitTorrent Traffic, Seeding Impossible". Archived from the original on xi Oct 2013. , TorrentFreak, 17 August 2007.
- ^ Broache, Anne (27 March 2008). "Comcast and BitTorrent Agree to Interact". News.com. Archived from the original on 9 May 2008. Retrieved 9 July 2012.
- ^ Soghoian, Chris (iv September 2007). "Is Comcast'due south BitTorrent filtering violating the law?". Cnet.com. Archived from the original on 15 July 2010. Retrieved 9 July 2012.
- ^ "BEP12: Multitracker Metadata Extension". BitTorrent Inc. Archived from the original on 27 December 2012. Retrieved 28 March 2013.
- ^ "P2P:Protocol:Specifications:Multitracker". wiki.depthstrike.com. Archived from the original on 26 March 2014. Retrieved thirteen November 2009. [ dubious ]
- ^ Johnston, Casey (ix December 2008). "Arstechnica.com". Arstechnica.com. Archived from the original on 12 December 2008. Retrieved ix July 2012.
- ^ Van Der Sar, Ernesto (four Dec 2009). "Thunder Blasts uTorrent'southward Market Share Away". TorrentFreak. Archived from the original on 7 December 2009. Retrieved 15 September 2011.
- ^ "uTorrent Dominates BitTorrent Client Market Share". TorrentFreak. 24 June 2009. Archived from the original on three April 2014. Retrieved 25 June 2013.
- ^ "Windows Public File Sharing Market Share 2015". opswat. Archived from the original on fourteen April 2016. Retrieved 1 April 2016.
- ^ Henry, Alan. "Most Popular BitTorrent Client 2015". lifehacker. Archived from the original on 9 April 2016. Retrieved ane April 2016.
- ^ "Torrent Server combines a file server with P2P file sharing". Turnkeylinux.org. Archived from the original on vii July 2012. Retrieved 9 July 2012.
- ^ Anderson, Nate (1 February 2007). "Does network neutrality mean an stop to BitTorrent throttling?". Ars Technica, LLC. Archived from the original on 16 Dec 2008. Retrieved 9 February 2007.
- ^ Mark (7 May 2020). "How to Stream Movies and Download Torrent Files in Brave Browser". Browser Pulse. Archived from the original on 9 October 2020. Retrieved six October 2020.
- ^ "What extensions are built into Brave?". Dauntless Help Center. Archived from the original on 8 Jan 2022. Retrieved eight January 2022.
- ^ Bahgat, Alessandro (x October 2008). "BitLet - Bittorrent applet". Alessandro Bahgat. Archived from the original on 21 November 2021. Retrieved 8 January 2022.
- ^ See for example "8 Legal Uses for BitTorrent". 17 August 2013. Archived from the original on 5 May 2021. The Net Archive
- ^ "Sub Pop folio on BitTorrent.com". Archived from the original on 14 January 2007. Retrieved 13 December 2006.
- ^ "DGMlive.com". DGMlive.com. Archived from the original on eleven November 2013. Retrieved ix July 2012.
- ^ "VODO – About...". Retrieved xv April 2012. (WebCite).
- ^ Cory Doctorow (15 Oct 2009). "Vodo: a filesharing service for film-makers". Boing Boing. Happy Mutants LLC. Retrieved fifteen April 2012. (WebCite)
- ^ Ernesto. "Pioneer One, The BitTorrent Exclusive Boob tube-Series Continues". TorrentFreak. Retrieved xv Apr 2012. (WebCite)
- ^ "CBC to BitTorrent Canada'south Next Great Prime Government minister". CBC News. 19 March 2008. Archived from the original on 14 June 2010. Retrieved 19 March 2008.
- ^ "Bittorrent" (in Norwegian). Nrkbeta.no. 2008. Archived from the original on 24 Oct 2013. Retrieved 7 April 2013.
- ^ "Torrents uploaded by EeuwvandeStad". MiniNova. 2009. Archived from the original on iv Nov 2013. Retrieved seven Apr 2013.
- ^ Denters, M. (eleven August 2010). "Tegenlicht – Download California Dreaming". VPRO.nl. Archived from the original on 26 March 2014. Retrieved seven April 2013.
- ^ Bol, M. (1 October 2009). "Tegenlicht – VPRO gemeengoed" (in Dutch). VPRO.nl. Archived from the original on 26 March 2014. Retrieved seven Apr 2013.
- ^ "Announcements about S3 BitTorrent discontinuation shouldn't exist buried in the commit history · Effect #27 · awsdocs/amazon-s3-userguide". GitHub. Archived from the original on 30 September 2021. Retrieved 30 September 2021.
- ^ "Periodic update - 2021-05-13 · awsdocs/amazon-s3-userguide@0d17598". GitHub. Archived from the original on thirty September 2021. Retrieved xxx September 2021.
- ^ "Using BitTorrent with Amazon S3 - Amazon Simple Storage Service". thirteen June 2020. Archived from the original on 13 June 2020. Retrieved 30 September 2021.
- ^ "Blizzard Downloader". Curse Inc. 4 November 2010. Archived from the original on 26 March 2014. Retrieved 4 November 2010.
- ^ "Globe of Tanks FAQ". Wargaming. xv December 2014. Archived from the original on 18 December 2014. Retrieved xv Dec 2014.
- ^ MJ Guthrie (11 March 2013). "EVE Online reconfiguring launcher to use BitTorrent". Massively.joystiq.com. Archived from the original on 13 Feb 2014. Retrieved 7 April 2013.
- ^ CCP Games (twenty July 2010). "All quiet on the EVE Launcher front end? – EVE Customs". Community.eveonline.com. Archived from the original on xiii March 2013. Retrieved 7 April 2013.
- ^ "Complete Download Options Listing – BitTorrent". Ubuntu.com. Archived from the original on 24 April 2010. Retrieved 7 May 2009.
- ^ "BitTorrent Sync engineering". Archived from the original on 30 August 2013. Retrieved 29 August 2013.
- ^ HM Regime (four September 2012). "Combined Online Information System". Data.Gov.United kingdom of great britain and northern ireland Beta. Controller of Her Majesty's Stationery Role. Archived from the original on 26 March 2014. Retrieved 7 September 2012.
- ^ Ernesto (iv June 2010). "Great britain Government Uses BitTorrent to Share Public Spending Information". TorrentFreak. Archived from the original on 27 October 2013. Retrieved 7 September 2012.
- ^ "HPC Data Repository". Florida Land University. Archived from the original on ii Apr 2013. Retrieved 7 April 2013.
- ^ Costa, Fernando; Silva, Luis; Fedak, Gilles; Kelley, Ian (2008). "Optimizing the data distribution layer of BOINC with Chip Torrent". 2008 IEEE International Symposium on Parallel and Distributed Processing. IEEE International Symposium on Parallel and Distributed Processing, 2008. IPDPS 2008. IEEE. p. ane. doi:10.1109/IPDPS.2008.4536446. ISBN978-one-4244-1693-half dozen. S2CID 13265537. (registration required)
- ^ "Torrents Help Researchers Worldwide to Study Babies' Brains". Torrent Freak. 3 June 2017. Archived from the original on 5 Jan 2018. Retrieved four Jan 2018.
- ^ "Academic Torrents Website". Archived from the original on vii May 2020. Retrieved four May 2020.
- ^ Miccoli, Fräntz (2014). "Bookish Torrents: Bringing P2P Engineering to the Academic World". MyScienceWork. Archived from the original on 26 July 2020. Retrieved 6 May 2020.
- ^ Ernesto (25 June 2010). "Facebook Uses BitTorrent, and They Love It". Torrent Freak. Torrent Freak. Archived from the original on nineteen April 2014. Retrieved seven September 2012.
- ^ Ernesto (ten Feb 2010). "Twitter Uses BitTorrent For Server Deployment". Torrent Freak. Torrent Freak. Archived from the original on 26 March 2014. Retrieved 7 September 2012.
- ^ Ernesto (16 July 2010). "BitTorrent Makes Twitter's Server Deployment 75x Faster". Torrent Freak. Torrent Freak. Archived from the original on 26 March 2014. Retrieved 7 September 2012.
- ^ a b Ernesto (seven August 2012). "Net Annal Starts Seeding i,398,875 Torrents". TorrentFreak. Archived from the original on 8 August 2012. Retrieved 7 Baronial 2012.
- ^ "Hot List for bt1.united states.archive.org (Updated August seven, 2012, 7:31 pm PDT)". Archived from the original on 3 August 2012. Retrieved viii August 2012. . Annal.org.
- ^ "Welcome to Archive torrents". Archived from the original on nineteen January 2016. Retrieved 22 December 2015. . Archive.org. 2012.
- ^ "AT&T Patents System to 'Fast-Lane' BitTorrent Traffic". TheStack.com. eight May 2006. Archived from the original on 23 February 2015. Retrieved 5 March 2015.
- ^ "FAQ:Modems/routers that are known to take problems with P2P apps". uTorrent.com. Archived from the original on 13 September 2008. Retrieved vii April 2013.
- ^ Halkes, Gertjan; Pouwelse, Johan (2011). Jordi Domingo-Pascual; et al. (eds.). UDP NAT and Firewall Puncturing in the Wild. NETWORKING 2011:10th International IFIP TC 6 Networking Conference, Valencia, Espana, May 9–13, 2011, Proceedings. Springer. p. vii. ISBN9783642207976. Archived from the original on ix May 2013. Retrieved seven Apr 2013.
- ^ "Is torrenting safe? Is it illegal? Are you likely to be caught?". 29 Nov 2018. Archived from the original on half-dozen October 2018. Retrieved five Oct 2018.
- ^ "The Piratebay is Down: Raided by the Swedish Police force". TorrentFreak. 31 May 2006. Archived from the original on xvi Apr 2014. Retrieved 20 May 2007.
- ^ "Technical report: An Estimate of Infringing Use of the Internet" (PDF). Envisional. i January 2011. Archived (PDF) from the original on 25 Apr 2012. Retrieved 6 May 2012.
- ^ "BitTorrent: Copyright Lawyers' Favourite Target Reaches 200,000 Lawsuits". The Guardian. 9 August 2011. Archived from the original on 4 December 2013. Retrieved x Jan 2014.
- ^ Albanesius, Chloe (30 Apr 2012). "U.K. High Court Orders ISPs to Block The Pirate Bay". PC Mag. Archived from the original on 25 May 2013. Retrieved half-dozen May 2012.
- ^ Adamsky, Florian (2015). "P2P File-Sharing in Hell: Exploiting BitTorrent Vulnerabilities to Launch Distributed Cogitating DoS Attacks". Archived from the original on 1 Oct 2015. Retrieved 21 August 2015.
- ^ Berns, Andrew D.; Jung, Eunjin (EJ) (24 April 2008). "Searching for Malware in Flake Torrent". Academy of Iowa, via TechRepublic. Archived from the original on 1 May 2013. Retrieved 7 April 2013. (registration required)
- ^ Vegge, Håvard; Halvorsen, Finn Michael; Nergård, Rune Walsø (2009). Where Only Fools Dare to Tread: An Empirical Report on the Prevalence of Zero-Day Malware (PDF). 2009 Fourth International Conference on Internet Monitoring and Protection. IEEE Computer Guild. p. 66. doi:10.1109/ICIMP.2009.xix. ISBN978-1-4244-3839-half-dozen. S2CID 15567480. Archived from the original (PDF (orig. work + pub. paper)) on 17 June 2013.
Further reading [edit]
- Pouwelse, Johan; et al. (2005). "The Bittorrent P2P File-Sharing System: Measurements and Analysis". Peer-to-Peer Systems IV. Lecture Notes in Informatics. Vol. 3640. Berlin: Springer. pp. 205–216. doi:10.1007/11558989_19. ISBN978-three-540-29068-1 . Retrieved four September 2011.
- Czerniawski, Michal (20 December 2009). "Responsibleness of Bittorrent Search Engines for Copyright Infringements". SSRN. doi:10.2139/ssrn.1540913. SSRN 1540913.
- Cohen, Bram (16 February 2005). "Under the hood of BitTorrent". Computer Systems Colloquium (EE380). Stanford University.
External links [edit]
| | Wikimedia Commons has media related to BitTorrent. |
- Official website

- Specification
- BitTorrent at Curlie
- Unofficial BitTorrent Protocol Specification v1.0 at wiki.theory.org
- Unofficial BitTorrent Location-aware Protocol ane.0 Specification at wiki.theory.org
Source: https://en.wikipedia.org/wiki/BitTorrent
0 Response to "Machine Trades Print Reading 6th Edition Torrent"
Post a Comment